Use dark theme by default
OK you have my upvote
Use dark theme by default
OK you have my upvote
it used to be cheaper, and with an audio jack. Add some environment and social consideration and I see many reasons to buy it.
Or you can buy a Google phone from Amazon and text about privacy or freeing Palestine while sipping your Starbucks coffee in your Tesla car.
Not everything has to be about how much do you personally get for the money you give.
I am so glad I could get the Faiphone 3 while it still had an audio jack. At that time the hardware was not too far behind, still too much for my use which is mainly scrolling through obscure left-ish forums and YouTube channels (thanks newpipe) and startups late-stage capitalist hacker news (I don’t know any better about tech).
I don’t see any cycle here, qemu-deskyop needs qemu-base and that’s it.
I think you meant that qemu-desktop is orphan.
EDIT: I am back on my pc so I can share a magic command to clean your orhpan packages (stares at electron) -> sudo pacman -Qdtq | sudo pacman -Rn -


knowing nothing about the situation is indeed the problem. if only this process was more transparent…
Are we implying that we should tap every phone call?
We can say a lot of very bad stuff over the phone too. Should we have a way to prevent this?
yes bare git works just fine. if you ever want a web GUI and/or issues and Pull Request you want such a tool.
A web GUI can be very nice to share your repository publicly. You can also use codeberg.org if you can’t or don’t want to self host.
PS : I’m kinda shocked (not that much) by the downvotes or your legitimate and polite comment. Still looking for better communities/system.
ok, thanks for the precision. I am interested in those projects and was looking at system76’s code. This new version is in a different repository named cosmic-epoch. I’ll dig it more.
COSMIC is built from GNOME shell, it is 100% a GNOME desktop and not from scratch.


I will never understand people using 3rdparty MQ and RPC implementations. What a a PR for rocketMQ right here.
You can and you should implement your communication protocols, most of the time 3rdparties are very wasteful and a security liability. I like ZeroMQ (https://zeromq.org/), they have amazing tech guides (https://zguide.zeromq.org/). I still mostly do my own code.
I may have trust issues but sockets are not THAT hard, they’re just amzaingly frustrating to debug, not as much as debuging 3rdparty code.
I had the idea that moderation is instance based in Lemmy, mods only moderate people on their instance.
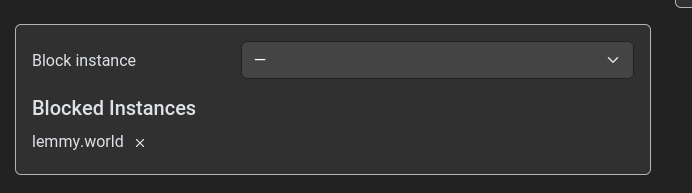
I must be missing something (I can see the community is not from lemmy.world but the guy is)


OK I got it, you are completely out of the loop here.
You do not grasp the idea of NoScript and other JS filtering extension. This is not about server code, your all arguments is baseless here.
By the way JS refered to Javascript and not NodeJS.
Anyway I got you whole company/business talk about “keeping the service available, secure, performant” and “GDPR […] bankrupting fine”… yeah lemmy.world.


Thanks for your answer.
First I don’t even grasp what a “service owner” is.
Second, for JS front-end openness there are already a bunch of app (web, android) that are open-source and secured. Everything has dependencies nowadays, this doesn’t prevent good security. Think all the python app and their dependencies, rust, android… even c\c++ packages are built with dependencies and security updates are necessary (bash had security issues).
I think with JS scripts it’s actually even easier to have good security because the app is ran in our web browser so the only possible attacker is the website we are visiting itself. If they are malicious then the close-sourced JS script is even worse. Unless you count 3rd party scripts embedded that bad dev uses in their website without even thinking about trusting them. That is also awful in both open or close source environment.
So even having imperfect security (which happens regardless to openness), who is the attacker here? I would rather run js script on my end if the code can be checked.


I believe you missed the point, I am not in defense of Security through obscurity (https://en.wikipedia.org/wiki/Security_through_obscurity), quiet the opposite.
The point: “[…] risk for the service owner as it gives an easily parsable way for an attacker to check […]” is well known and not the discussion here. You can choose close source for ‘security’ this is opensource community so I am wondering about such a tool.


There’s no “open source” centralized website. You can’t know what the server is effectively running unless you have access to it. To me this makes no sense.


The irony
And C++, just checked the wiki and the 2 example of openssh’s heartbleed and sudo, both in C. Not C++. As expected.
I’m not sure why people keep pushing that myth on C++. It’s been a decade we have smart pointers. There’s no memory management to be done ever.
Using the old ‘new’ is like typing ‘unsafe’ in rust. Even arrays/vectors have safe accessor.
Am I missing something?
hosted on GitHub, the irony…