I’m considering implementing SELinux in my Debian setup, but I’ve read that it was initially developed by the NSA.
Can anyone shed any light on this? Has SELinux been audited? When and by whom? Does the NSA still have anything to do with SELinux, or is this a “US Navy creating Tor” sort of scenario?
I have no concerns about it.
- It is well-known.
- It is completely open.
- It has been in wide use for decades.
- In that time, there has never been a reason to believe it’s malicious.
- It is not an encryption tool, but an add-on for denying actions that would otherwise be allowed.
It’s not unusual for US government agencies to develop or fund technologies that end up used by the whole world. The internet is another example.
Also one other great example is GPS. Just like SELinux it is very well understood and open.
It’s a "the NSA wanted to have that for their own internal use” kind of scenario.
Not an expert, so feel free to correct me but…
Selinux is open source https://github.com/SELinuxProject/selinux
Selinux is built into the kernel already. So if it has NSA spyware, you’re already compromised.
I’m unaware of any ‘official’ audit.
Using it should only increase your security.
If you’re in the position that the NSA is in your system trying to bypass SELinux, you have much bigger problems.
Besides, in that case, having it disabled is going to make it easier for them anyway.
One question and some unfollowable advice.
Question: Why not use AppArmor? My understanding is that’s what Debian uses by default instead of Selinux which is more native to Enterprise Linux (Fedora, RHEL, Rocky, Alma etc).
Unfollowable advice: As an EL admin where it’s the default and very closely integrated, we have a saying; “It’s not always dns, mostly it’s Selinux”. For most distro-sourced software, it’s fine. But if you install software from other sources, you’re going to hit problems.
Others have given good reasons to your specific questions, but one tip if you go down this route. We use a redhat tool, “setroubleshoot-server” which helps hugely in both identifying when something isn’t working because SELinux has blocked it, but also gives you the commands to add an explicit rule to allow it, so you can view the log, understand why it’s blocking, and allow it without needing to get too involved with the complicated file contexts.
Sadly, it looks like this tool isn’t available in Debian, which would seem to make like a lot harder using selinux. Familiar as I am with selinux, I don’t run it on my personal servers or this laptop, which are Debian.
Thanks for the advice!
SELinux has been GPL for 24 years.
It’s part of what was called Rainbow Books, but is known more widely these days as the Common Criteria.
https://en.wikipedia.org/wiki/Common_CriteriaIt’s the “Government setting standards” sort of scenario.
It’s worth noting that SE Linux takes considerable knowledge to administer correctly in many scenarios, and can lead to some strange problems if you don’t know what you’re doing. Definitely worth learning about, though.
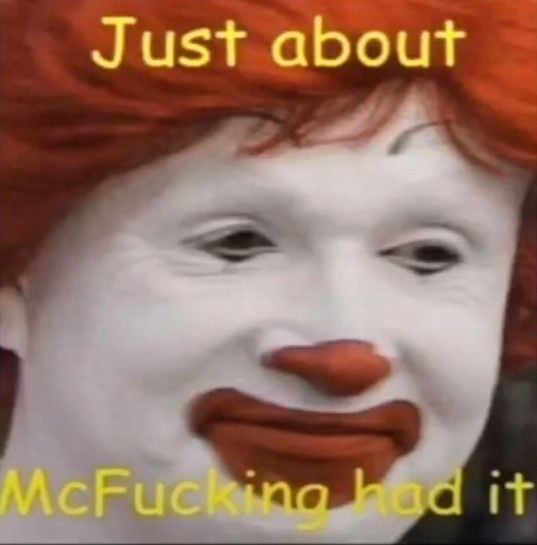
SELinux: Tries doing a thing, didn’t work Spend eight hours trying various crap. setenforce 0 Works now Five minutes cussing 30 seconds googling how to set the context Works forever
Tries doing a thing…
Yeah it’s really not that difficult once you get the basic concepts, then it’s navigating your own maze of rules :p
Things like ausearch, aureport, audit2allow make light work of it.